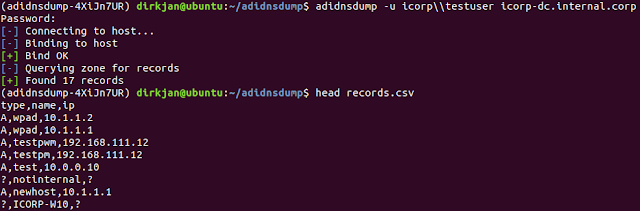
By default any user in Active Directory can enumerate all DNS records in the Domain or Forest DNS zones, similar to a zone transfer. This tool enablesenumeration and exporting of all DNS records in the zone for recon purposes of internal networks.
For more info, read the associated blog post.
Install and usage
You can either install the tool via pip with pip install adidnsdump or install it from git to have the latest version:
or
Code:
pip install git+https://github.com/dirkjanm/adidnsdump#egg=adidnsdump
GitHub - dirkjanm/adidnsdump: Active Directory Integrated DNS dumping by any authenticated user
Active Directory Integrated DNS dumping by any authenticated user - GitHub - dirkjanm/adidnsdump: Active Directory Integrated DNS dumping by any authenticated user
Installation adds the adidnsdump command to your PATH. For help, try adidnsdump -h. The tool can be used both directly from the network and via an implant using proxychains. If using proxychains, make sure to specify the --dns-tcp option.